por Rebeca | Jun 9, 2021 | Ciberseguridad, Soffid
The 2020 Global State of Least Privilege Report (Least Privilege Technologies and Solutions) shows that two-thirds of organizations now consider the implementation of least privilege a top priority in achieving a zero-trust security model.
Below, we take a look at some of the critical drivers for the adoption of least privilege Solutions and Technologies. We also explore the failure of traditional systems and how modern solutions such as Software-Defined Perimeter, Secure Web Gateway and Risk-Based Authentication, among others, engender greater enterprise network security.
Access is Responsibility and Least Privilege Technologies and Solutions

According to an Identity Defined Security Alliance (IDSA) study published last year, 79% of enterprises experienced an identity-related security breach in the previous two years. Last year, just as the COVID-19 pandemic gathered momentum, another report revealed a rise in attacker access to privileged accounts, which puts businesses at a greater risk.
It is important to note that in this age where data is everything, access is equal to responsibility. Therefore, the greater access a person has at a given moment; the greater responsibility they have to protect the data that they have access to. According to the State of Security blog, author Anastasios Arampatzis states that the central goal of privilege access management, which he admits covers many strategies, is the enforcement of least privilege.
Privileged accounts are a liability precisely because the data they have access to makes them attractive targets to cyber attackers. The greater the level of access an account has, the more significant the impact of an attack would be. More so, the greater the number of privileged accounts on a network, the more catastrophic an account compromise could be. Basically, every additional privileged account multiplies the risks on a network. Therefore, it is crucial to keep the circle of privilege small in order to limit unnecessary data exposure.
Legacy Systems: The Failure of VPNs to Adequately Secure
Amidst the current challenges in privileged access management, organizations are beginning to explore alternative solutions to traditional VPN technology and other legacy security solutions which have failed in actively securing privileged accounts. One notable problem is the lack of remote user security on many VPN products, and they neither integrate well with identity providers nor properly implement user policies on identity access and authorization. The weakness of VPNs are made more apparent in this age of remote work.
Least Privilege Technologies and Solutions
At the turn of the pandemic, companies had to allow their employees to work from home. This led to a surge in VPN adoption. According to the Global VPN Adoption Index report; VPN downloads reached 277 million in 2020 based on data collected from 85 selected countries.
The cybersecurity landscape can be described as a kind of cat-and-mouse race. In response to this trend, cyber attackers shifted their focus to exploiting VPNs, amongst other techniques such as phishing. However, being a legacy technology that has somehow due to its ubiquity made its way to more modern times, VPNs have become quite weak; based on the assertion that “VPNs are designed to secure data in transit, not necessarily to secure the endpoints. ” it is easy to see why the ‘new normal’ in cybersecurity is the protection of endpoints in an age where data is gold.
Least Privilege Solutions and Technologies
The current overhauling of our approaches to access management and authentication; has given birth to the rising adoption of the cybersecurity of least privilege. This principle is connected to another swelling trend in cybersecurity: the zero-trust model.
True zero trust technologies adopt the principle of least privilege by default.
The need for privileged accounts is common to most information systems. These accounts are necessary to perform scheduled configuration and maintenance tasks, as well as supervening tasks such as the recovery of a hardware or software failure or the restoration of a backup. Due precisely to the need to use these accounts in an unplanned manner, their management must combine security, procedures and flexibility.
In order to effectively manage these accounts, the Soffid product has the necessary logic to Identify accounts. Classify them according to the level of risk and its scheme of use; distribution and assignment to responsible users, automatic and planned password change process. Passwords delivery process to authorized users and automatic injection of passwords, when this injection applies and makes sense.
Conclusion
The principle of least privilege in cybersecurity is not just an exciting fad that would go away soon. Rather, it is becoming a standard model and best practice for network protection in the new normal of cybersecurity.
Sources:
(1) Tripwire
(2) Security Tech

por Rebeca | May 26, 2021 | Ciberseguridad, Recursos, Soffid
Imagine this scenario about Future Trends in Access Management… – If you are the CEO of a mid-sized organization with branches in different continents and three thousand employees, how efficiently could you monitor logins? Perhaps, on a bad day, an employee would have lost their Smartphone or lost the paper in which they wrote the password.In such a case, would you identify that one illegal or criminal login from all the 3000 logins that day?
In this scenario, we are yet to find a universal solution to manage online identities in both the government and the private sector.
Since the IAM space is continuously evolving
Organizations identify new trends in Identity and Access Management to minimize data-breaches, meet regulatory requirements, and manage user identities to the utmost extent.

Years of data breaches stemming from credential theft, attacks targeting privileged user accounts and poor password practices have led to a major evolution in identity and access management technology designed to protect enterprise data.
Five IAM trends are addressing the need for greater user account and network protection.
Identity and Access Management (IAM) has the attention of cybersecurity professionals around the world. The identity and access management market growth has roughly quadrupled over just the last three years, and shows no signs of slowing down any time soon.
The COVID-19 pandemic has raised the visibility of identity & access management (IAM) due to the high priority in getting remote access secured and the increased protection needed around digital transformation initiatives.
In an effort to make organizations more secure, agile and resilient, IAM leaders must improve governance and strengthen privileged access management (PAM) practices to prevent breaches, establish more robust and agile authentication and authorization, and enhance consumer IAM to prevent fraud and protect privacy.
In this rapidly changing business scenario, here are upcoming trends that promise to revolutionize the IAM sector:
1) Adapting Biometrics
As per Global Market Insights, the global biometric market would reach an estimated value of USD 50 billion by the end of 2024. Perhaps one of the rapidly emerging trends in the IAM sector, biometrics like retinal scans, facial recognition systems, and fingerprints, is highly preferred for ensuring authorized users in networked systems.

To counterbalance this threat, the future trend would involve IAM, which relies on biometric data, to get an additional layer of security for protecting the biometric information.
2) Blockchain and Future Trends in Access Management
Blockchain offers features like transparency, reliability, and integrity, making it a popular choice for ensuring data protection with both public and private sectors.
While talking about Blockchain in the context of IAM; the two aspects, the come into play are – Audit trail and self-sovereign identity. Self-sovereign identity is the concept of an individual protecting their entire identity as their personal property rather than let an organization or third-party provider manage it. By keeping the individual’s information protected by encryption in a permanent blockchain across a distributed network system, this concept offers complete individual control over their identity data.
Through the Self-sovereign identity system, the idea is to replace centralized; identity providers and instead let each individual take control and decrypt the data only when required.
Audit trail, a user’s entire login history, access request, permission grants, changes performed, or engagement is recorded. This is helpful for an organization in monitoring activities, detecting fraud, and also meets compliance requirements.
3) Single Sign-On Systems and MFA
While MFA is one of the most popular IAM practices, there is still plenty of scope for its improvement; as data breaches still occur and cause substantial revenue losses. Adaptive Authentication is the advanced version of MFA. Which relies on machine learning capabilities to detect } user behavior or illegal entry.
Adaptive Authentication pulls in all the details of user login in terms of login time. Device, location, browser, and other data, which helps analyze a login attempt’s authenticity. Based on the analysis, if a login attempt turns out to be fishy. The system will ask the user to fill in an MFA to be authenticated.
Another popular IAM industry trend is Single Sign-on (SSO System) usage with MFA. That helps users leverage a unified, singular set of credentials to gain access to networks; data, applications, web, and the cloud.
4) IAM and the Internet of Things (IoT)
With the arrival of the Internet of Things (IoT), there is a massive requirement for Identity Access Management service. Whenever an IoT based device is added to a network, there increases the need to mitigate security risk.
Hence, the current priority is to ensure secure identity access management. On these IoT devices for restricting the entry of hackers into the network. Devices that can pose a threat could feature smart TVs, security cameras, and smart bulbs.
Another technology that could prove to be a breakthrough is working on IAM systems. Which require the system to authenticate a user’s access through numerous devices.
Also, in numerous cases, securing IoT devices would be achieved by embedding; the device identities in the processing chip and being an integral part of the hardware.
5) Artificial Intelligence in IAM
An aspect of Identity Management, Context-based identity, also is responsible for comparing data about. This data includes numerous behavioral patterns like physical location, IP address, usage, preferences, and machine address.
Leveraging AI programming algorithms for data mining helps discover data patterns. That are extremely helpful in reducing fraud and identifying risks. This technique has been highly useful in banking systems across the globe.
6) Identity Access Management for Cloud Services
Since the cloud is in great demand, organizations have been shifting to cloud. Services to provide advantages such as efficiency, scalability, and flexibility.
Namely, Access Management, Identity Management, Access Governance, and PAM. We help you elevate your organization’s goals towards digital transformation and help develop data strategies. In line with revenue maximization and achieve customer satisfaction.
(1) Gartner
(2) Search Security

por Rebeca | May 19, 2021 | Soffid
Código Abierto
Today’s business leaders face enormous pressure from markets, competition, and the current pandemic, which is radically changing the way we do business and engage with customers. Organizations need to adapt, imagine new revenue models, innovate as never before, and attract a new generation of talent to fuel this evolution and help the business stay relevant.
In the last few decades, organizations large and small have started leveraging the benefits of open source at unprecedented levels. One of the benefits of working with open source technologies or projects is the free sharing of ideas. Open source brings people together to brainstorm and develop a common piece of technology.

The open source web frameworks offer an alternative that shifts the company focus from the centralisation of resources – which has become of little significance – to the adoption of more internationally widespread technologies. The technological exclusive and the supposed guarantees of a private supplier are exchanged for a transparent shared standard.
In the past technology ownership guaranteed a competitive edge over the competition and money could also be made from licensing.
With the growth of the web and the spread of technologies to support the online services, the IT sector has experienced the formation of a very fragmented situation.
In this scenario the big digital service companies have played an important role, at times determining with their economic weight the growth of some of these technologies and the consequent decline of others. New international standards have been set.
At the same time
Many cases of successful open source frameworks have emerged which have ridden the wave of the community-driven technologies, i.e. developed and maintained by international teams of independent developers.

In light of the success obtained by these frameworks, today privatising the technologies on which to base their services. Also and products means companies run the risk of reinventing the wheel, rather than concentrating on activities that create solid value.
Compared to open source frameworks the owned ones are more expensive; and risk becoming outdated more quickly in a world in constant evolution.
The value of ideas has increased
A shared technological standard on an international level, helped by an open source philosophy; has a superior value compared to the in-house alternatives. The ability to integrate programming languages and different tools effectively and using the resources already created; by other developers increases the competitiveness of the web-based platforms.
Considering the rise of open source frameworks the question is not how to centralise control over technology. But how to adapt these resources to our advantage, participating in their progressive enhancement while developing components for company use.
Technology is the tool that allows us to drive value; but this comes from positive ideas to digitalise the company resources available.
With freemium solutions like Soffid, the customer get all the benefits from both sides; from the traditional product and from the open source product. But they get a good support, they get a development roadmap and quick security fixes.
Soffid is one Single product, release like open source and including all the features; about Identity and access management, priviledge account management and identity governance.
Shall we talk?

por Rebeca | May 13, 2021 | Sin Categoria
We have the pleasure to share with you Identity and Access Management Snacks by Soffid, our best topics in Identity and Access Management.ç
Come along to our new friendly «snacks» focused on the latest trends in digital identity
Learn how your users can securely take control over sharing their data and how identity can not just solve these challenges but be a business enabler too.
We’d love to hear your ideas for topics to discuss as well!
We’re always on the lookout for new trends in Identity and Access Management, so follow our Youtube channel and if you like this page, share it now!

por Rebeca | May 12, 2021 | Ciberseguridad, Recursos, Soffid
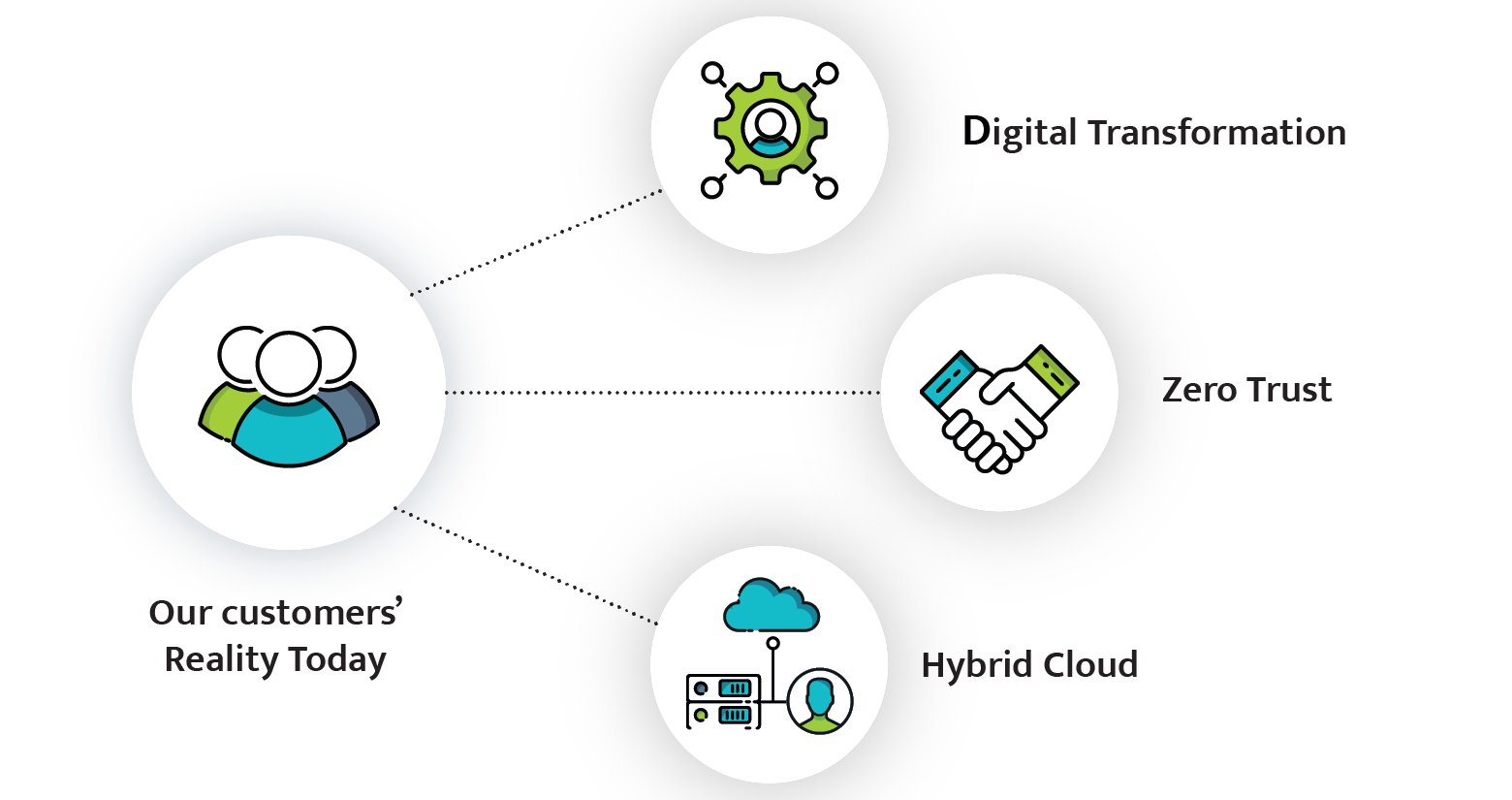
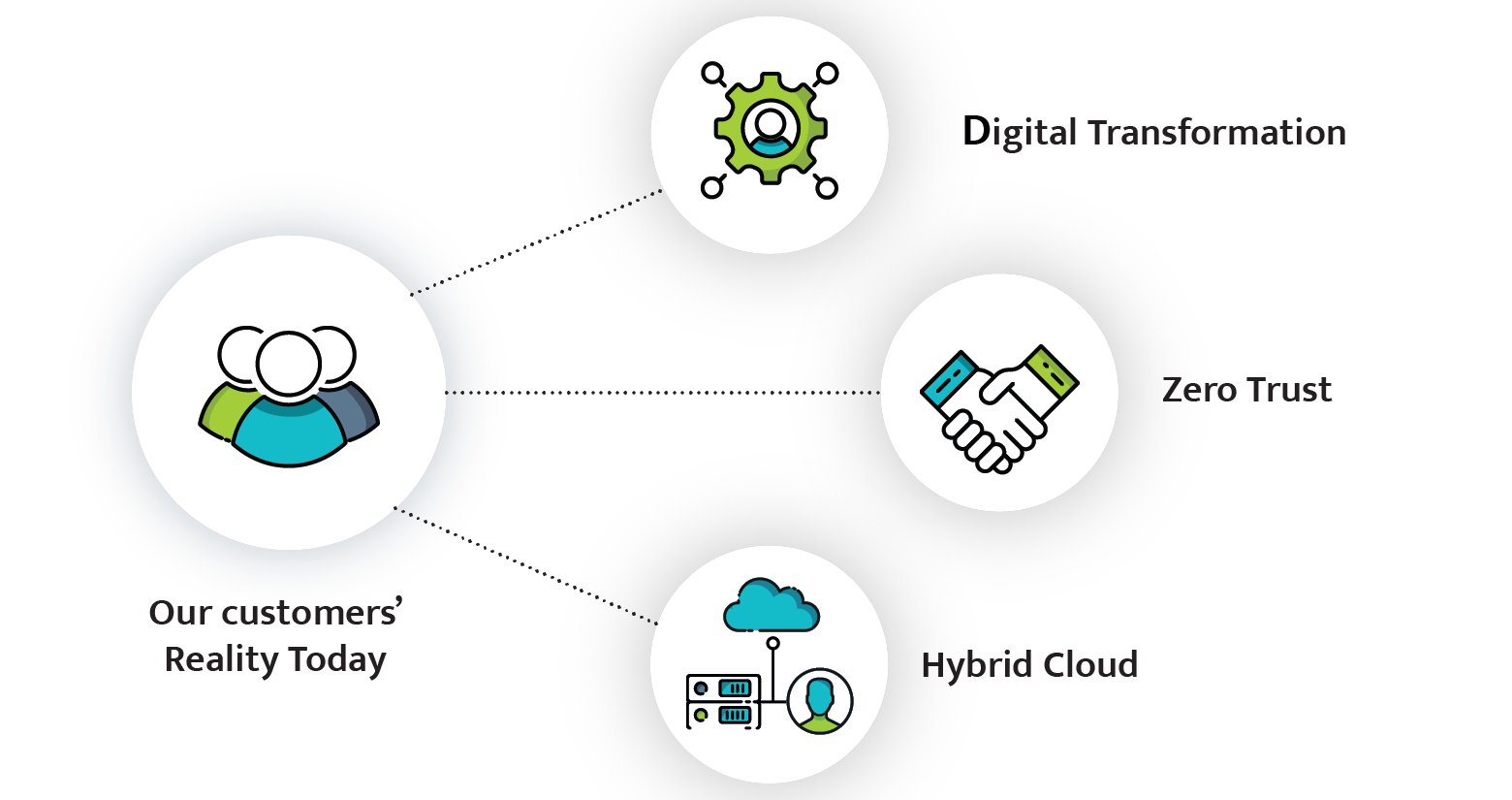
Digital transformation, Competitive advantage and saving money are driving factors for any organization moving to the cloud.
However, many organizations still need to support their business-critical applications that are running on premises.
To support and secure this reality and enable a smooth migration to the cloud, you need a comprehensive hybrid cloud IAM strategy today.

Hybrid is the reality of a lot of our customers. However, it is also a relative term.
For some customers, who have a lot of complex legacy and mission critical systems running on prem, hybrid cloud simply means moving from physical data centers that they manage to co-location data centers where they no longer manage the facilities and environmentals, but still handle everything inside the cage.
These are typically the customers that are at a scale where the cost of public cloud is more expensive than continuing to manage on their own. Or they are very risk averse and conservative in their approach to IT because they have regulatory or other security concerns.
And then we have customers who have a public cloud-first business mandate. Customers who are focused on delivering value to their users. As are those who want to take full advantage of the cloud to reduce time to market for any new service. These customers have fully embraced cloud and are looking for solutions with a cloud-first attitude.
No matter where a customer falls on the spectrum, to trends we discussed on the prior slide hold true.
When the company moving to the cloud, digital identity plays a very important role in all these trends. Also, it is very likely that no old identity solution will do.
You need an identity solution that can be placed at the heart of your business. Without leaving it flexible enough to meet a wide range of needs across the business. In addition, that you can drive exceptional digital experiences for customers, partners and employees. Not to forget, may it have the power and scale to handle Black Friday digital traffic volumes every day.
Customers need a true hybrid identity platform that can deliver on the needs of today, as well as in the future, as the technology landscape continues to evolve.
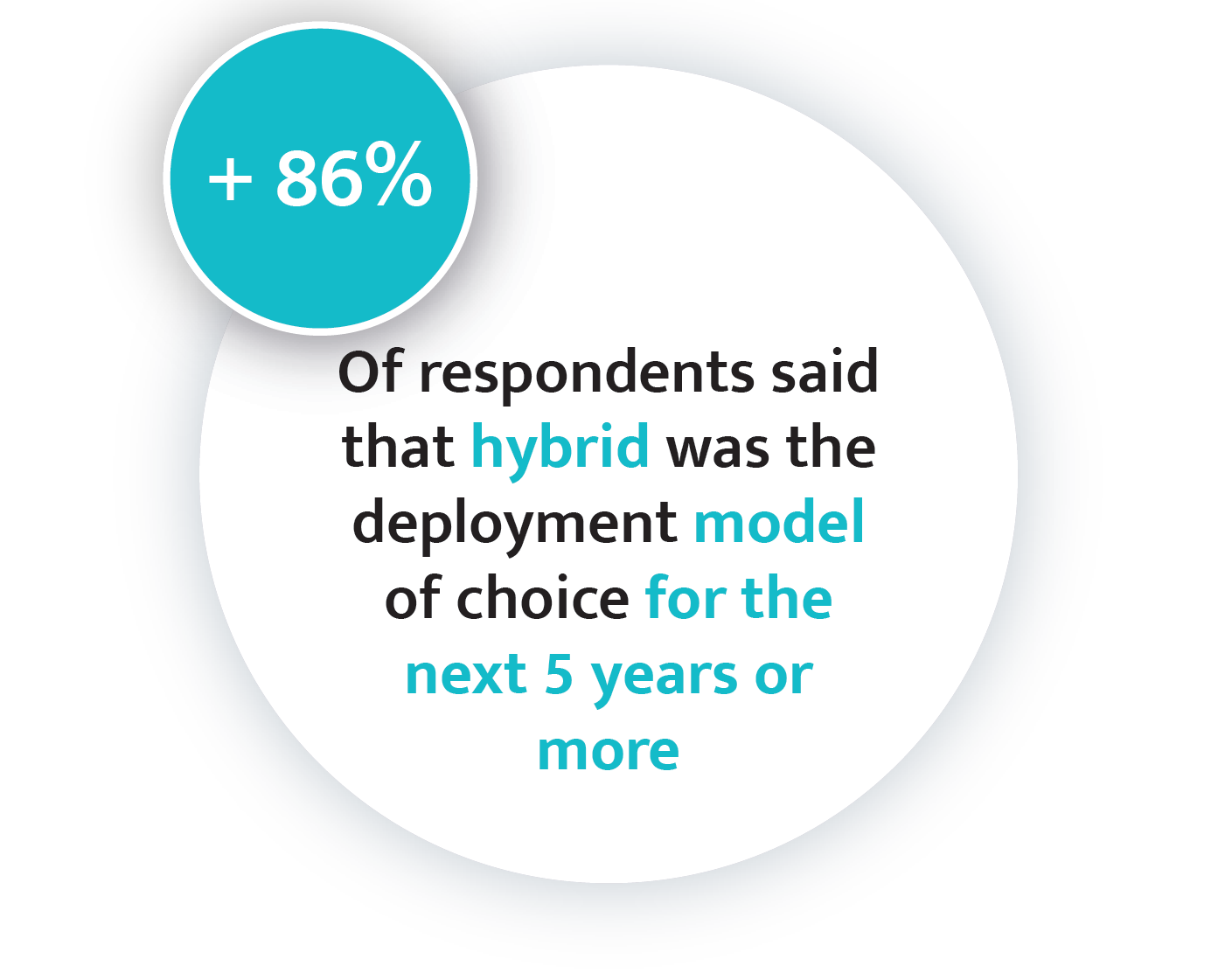
In fact, I ran a poll during Soffid identity live events last year, where a global audience was polled on this exact topic.
When asked how long that they see themselves running in such a hybrid cloud model, more than 86% of the respondents said that hybrid will be their reality for five years or more. These are all customers who are adopting cloud actively.
So what are the challenges that they face and why are they not able to move 100% to the cloud sonner?
Well, for these customers they’re ready to get the cost and the security benefits from cloud by moving their business-critical applications. But the biggest challenge is how to transition to the cloud from on premises, which they’ve invested in so heavily over many years, while still maintaining full functionality.
We believe we have a solution that helps you rise to the challenge of our new normal driven by digital transformation, Zero Trust, and hybrid cloud, as well as solve some of the associated problems that our teams are really struggling with.
A recent study found that more than 70% of IT leaders expect benefits from hybrid IAM, primarily in the areas of customer and employee experiences and security. This is important because, as discussed before, our belief is that organizations need an identity platform in order to address all the opportunities and challenges that our current environment presents. And furthermore, organizations need IT delivered from the cloud so that you can focus on meeting all the new demands, while resting assured that you have a solution that meets the needs of today, tomorrow and as well as into the future.
You need a platform that will be there for you as you grow and as your needs evolve.
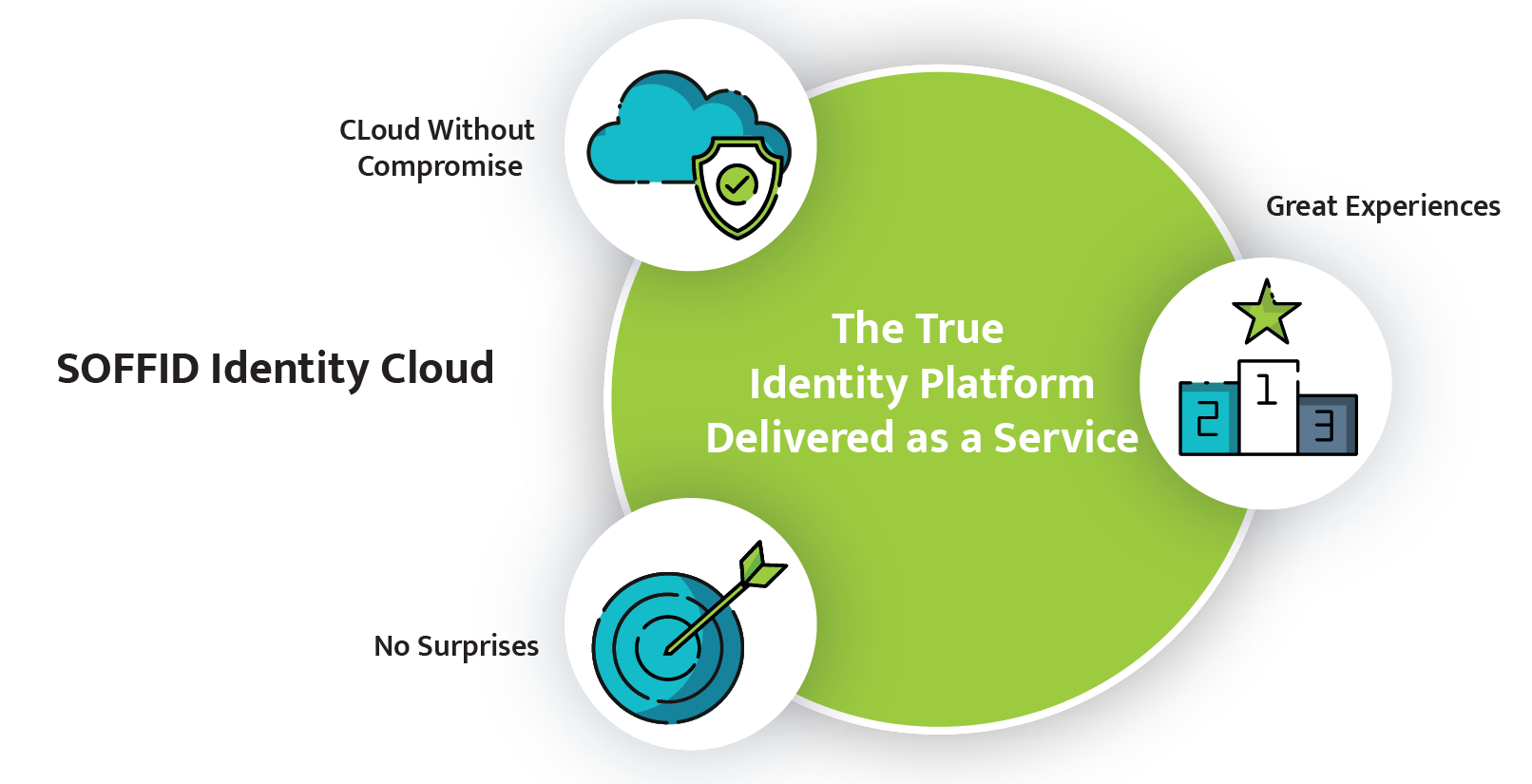
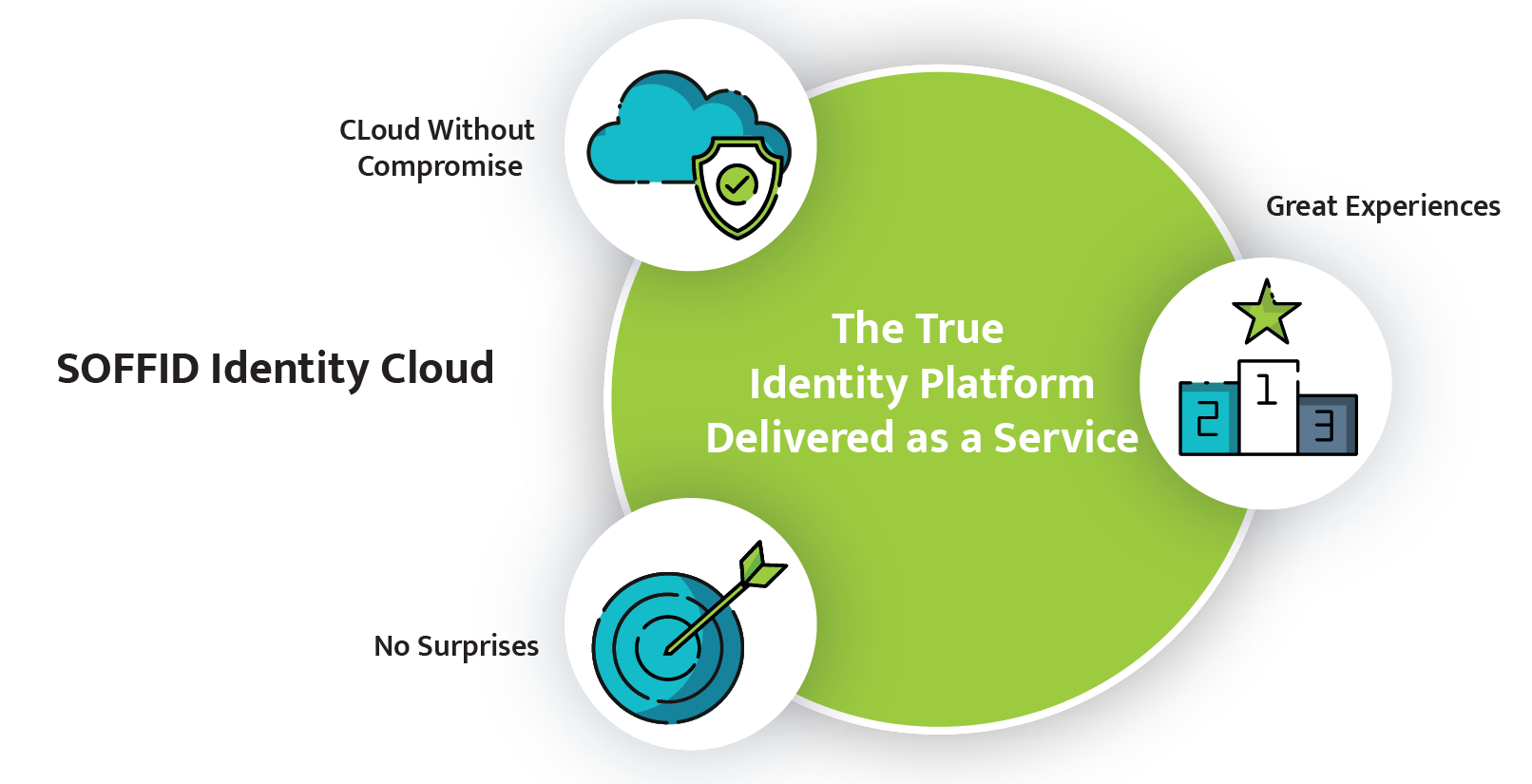
A true identity platform delivered as a service.
Soffid IAM Cloud offers cloud without compromise, no surprises, and great experiences for your customers, partners and employees. A platform that will be there for you as you grow and as your needs evolve. A true identity platform delivered as a service.
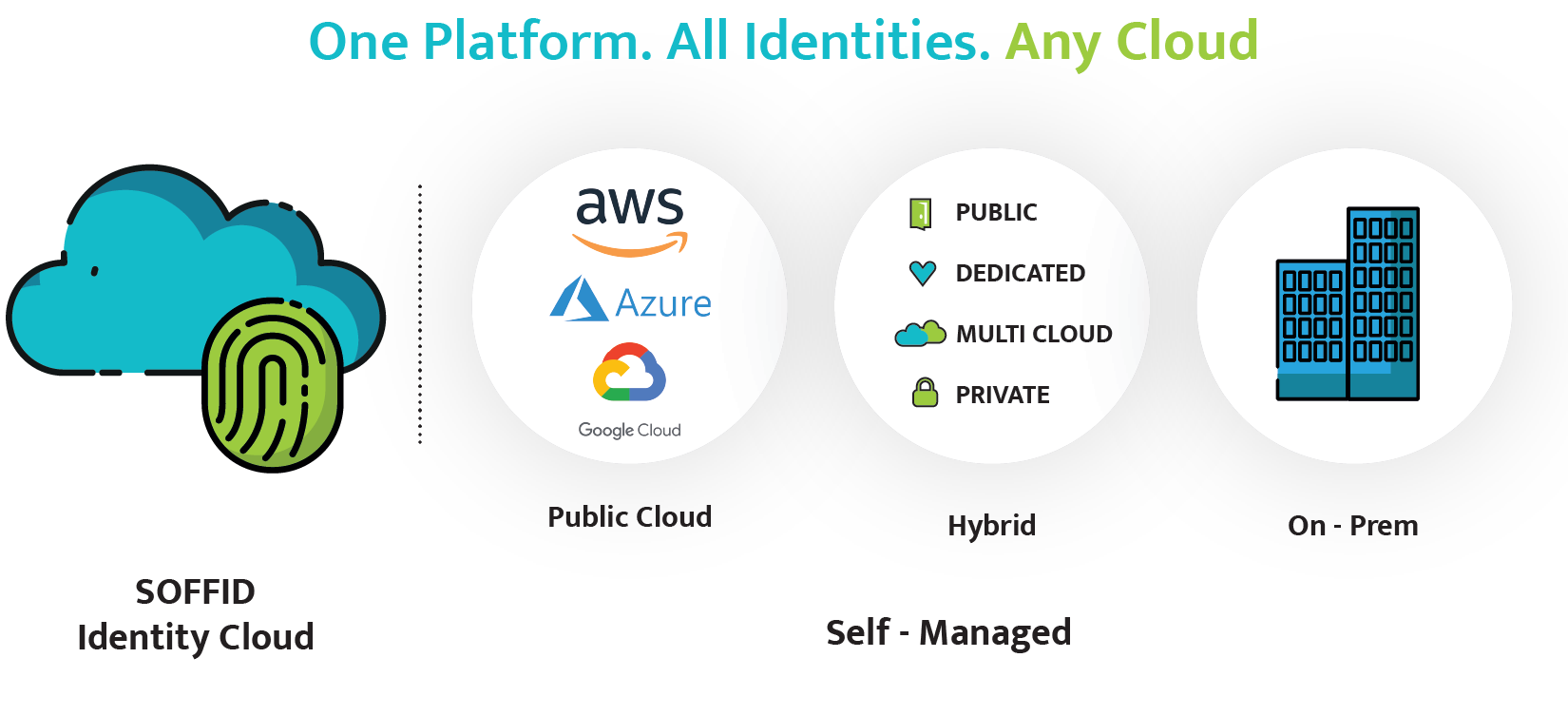
Let’s explore what I mean moving to the cloud without compromise. With one subscription, you get complete freedom to meet your full hybrid needs. Not only does this include our moving to the cloud solution but also powerful downloadable components that you can deploy into your enterprise to integrate all of your applications. No matter where they are, including on prem because is hybrid, which is a maximum deployment flexibility.
And you don’t need to compromise on getting a true identity platform. And no surprises here is what I mean, with a flexible subscription, you get predictable pricing. Which means no surprise overage charges because your user logged in more than originally projected. You are protected.
Certainly, you also get complete control of your data with complete isolation of your environment. You choose where your data is stored geographically so that you can comply with regulations. Your data is never commingled with other customers’ data and complete isolation means, no noisy or nosy neighbors affecting your service.
No surprises also means you get the power and scale of providing a consistent service to your users.
Finally with Soffid IAM Cloud you can deliver unparallized and optimized journeys for your users with our advanced intelligent access orchestration capability. With this you can go passwordless or even usernameless to provide the ultimate convenience for your users.
We support any identity type, customers, partners and employees and also devices which are becoming first-class citizens with IoT.

Now let’s take a look at how Soffid IAM Cloud can deliver real business value and benefits that are tangible. It can help you reduce your app development times by 25-95%. Plus, we can help you reduce your architecture planning and design time by 25-80%. Not to mention reducing IAM Ops overhead by 40-80%.
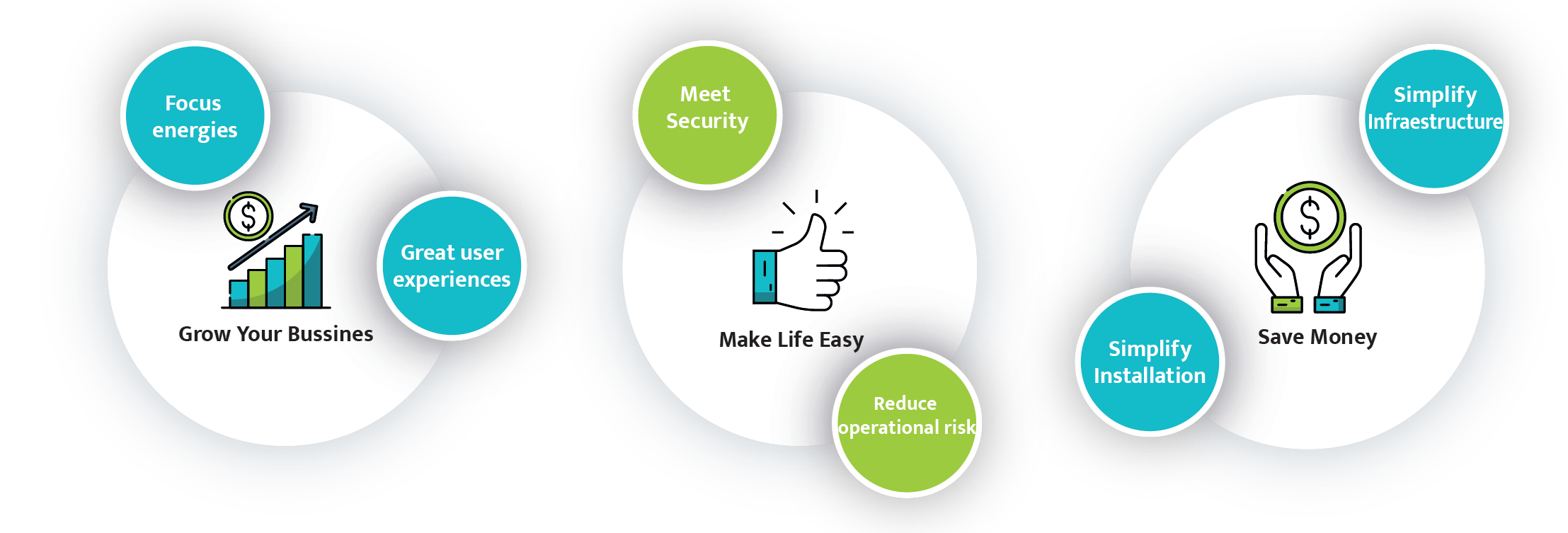
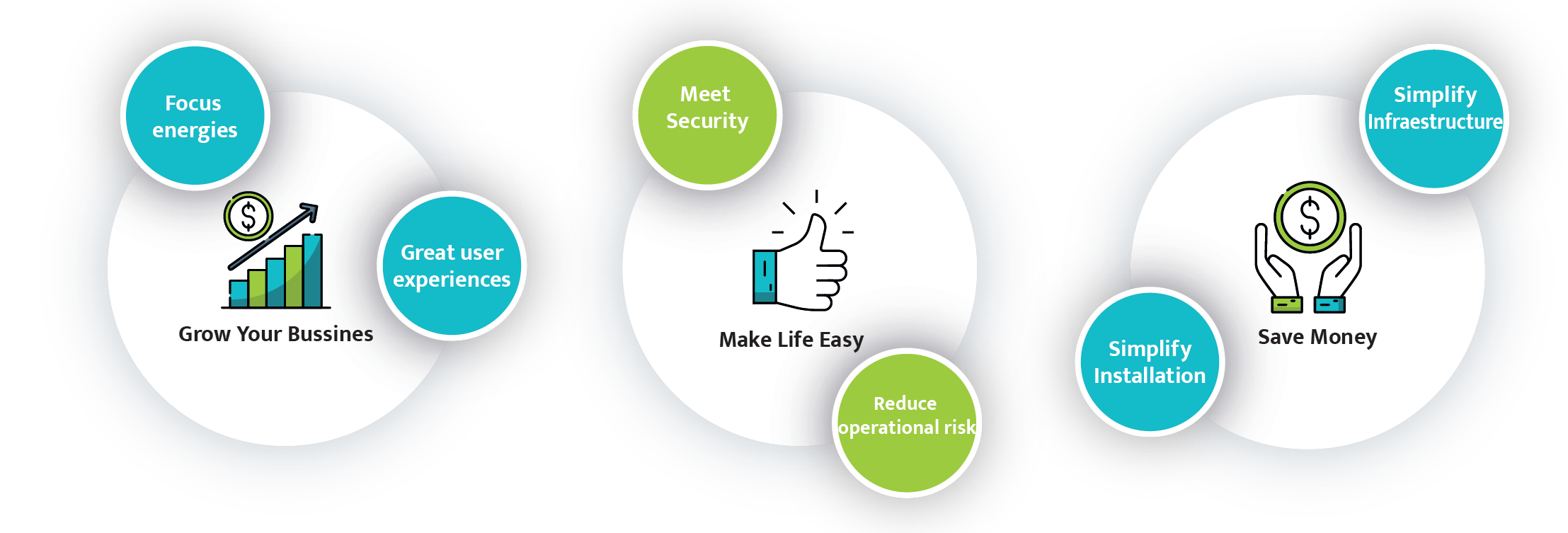
And that enables you to grow your business and it makes your life easy and saves money. Who wouldn’t want that? It means you can focus your energies providing great user experiences.
It means your applications developers can focus on what they do best, which is building great apps rather than worrying about IAM protocols like SAML and OAuth 2. They can quickly add capabilities like passwordless or even usernameless to the experiences with just a few clicks and focus their time on building your business IP.
One Platform. All identities. Any cloud
Also, it means that you can spend less time designing the security features of your apps. Because your identity and access management needs are handled by a single trusted vendor. This way you don’t have to worry about stitching together multiple products from different companies but rather reduce operational risk. And you can meet security regulatory and compliance requirements. Additionally, we do all of that while reducing your infrastructure needs.
You spend less time running systems and more time delivering value to the business and that’s just undeniable.
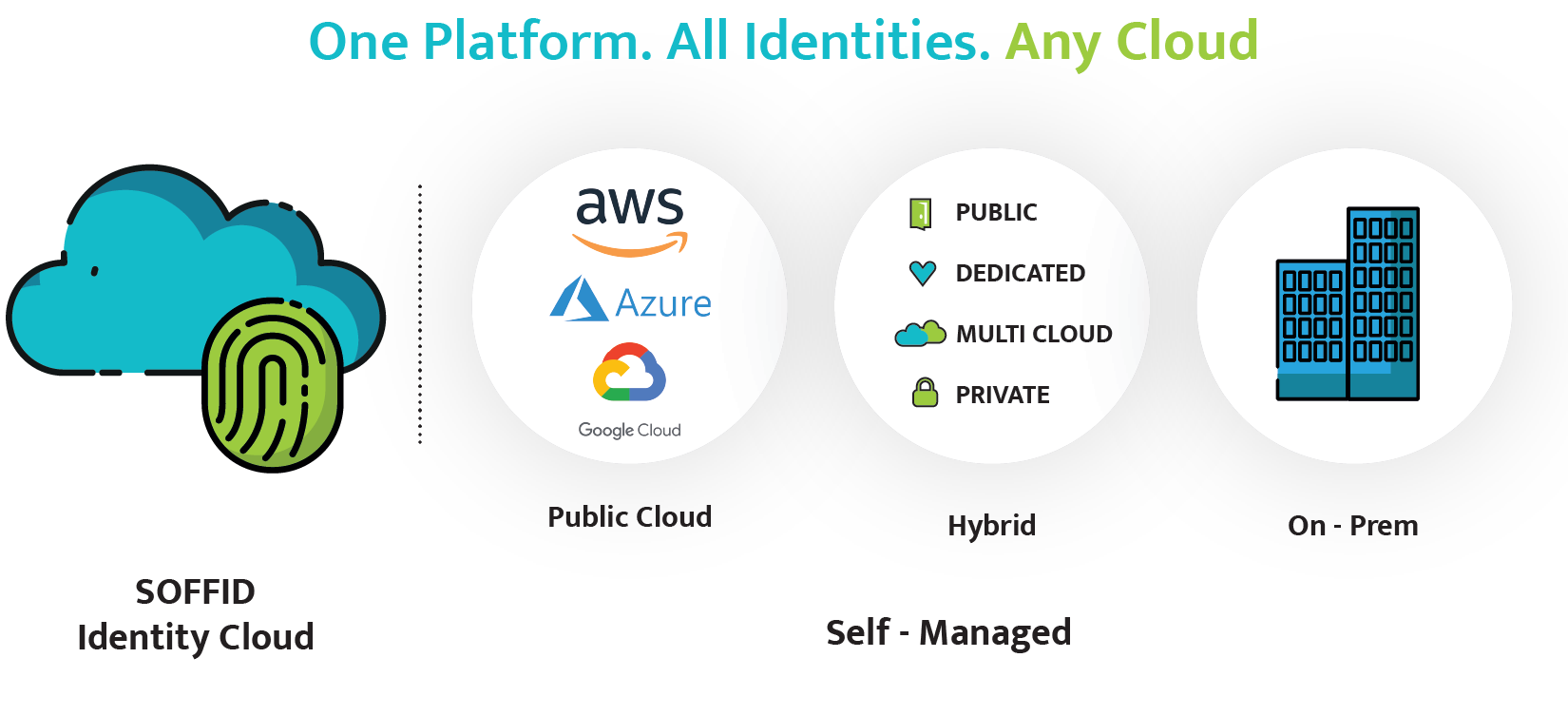
And you can do all this while leveraging Soffid IAM Cloud. However, if taking a different path to the cloud journey including your hybrid needs, we have another options as well and that includes our self-managed option. You can deploy this very rich platform on premises in any public cloud or in a hybrid fashion.